
AVAware Celebrates 15 Years of Innovation
Happy Holidays from all of us at AVAware Technologies
Dispelling the Myths!
Ensuring your PC is Running Optimally
AVAproject Tip: Creating Hardware Specifications using AVAproject – Part 2
|

|

|
|
|
AVAware Celebrates 15 Years of Innovation
On December 12th of this year, AVAware proudly celebrated fifteen years of developing innovative software solutions for the architectural openings industry.
On behalf of all of us at AVAware, we wish to thank all our valued clients, vendors and corporate partners for all their past and ongoing support. It’s only through cultivating relationships with so many other successful companies and individuals that we’ve been able to achieve success in our own endeavors.
We thank you all for the past fifteen years and look forward to many more years of success and innovation to come.

Paul Kirsch
President & CEO
|
|
|
|
|

|
Dispelling the Myths!
|

|
Over the past year, AVAware’s sales and support teams have heard some incredible stories; as the frequency of the stories increased it became apparent that we had to nip this situation in the bud. The following are a collection of some of our favorite misconceptions and questions on which we would like to set the record straight.
|
|
It’s inevitable that as a company and its products become more popular and widely used that myths and misconceptions begin to evolve. A large part of this is certainly due to the “broken telephone” effect, where information is skewed and details modified as people pass information amongst themselves. Sadly, another great contributor are the “less than scrupulous” competitors that resort to misinformation and outright lies to advance their products. One could argue that it’s somewhat flattering to think that others would expend the effort to perpetuate falsehoods simply to be able to compete, but this obviously does a huge disservice to everyone – especially the clients.

|
Is AVAproject built on Microsoft Excel?
|
Absolutely NOT!
Prior to the release of AVAproject in the late 1990s, detailing and estimating software all employed a similar “heading based” data entry model; Openings were entered in headings, as they would appear in a hardware schedule. In order to begin entering a project, the estimator would have to begin with a hardware specification that had all the opening information and hardware organized into headings.
AVAware innovated the spreadsheet model as an alternative that allowed the data entry process to be organized from several different starting points. Inspired by “synoptic journals”, AVAproject allowed estimators to begin a project with either the openings list or the hardware specification and move between them at will. Spreadsheets were used as a user interface model because of their flexibility and, more importantly, their familiarity. Almost everyone that had computer experience used a spreadsheet at some point. This helped make the product comfortable and dramatically reduced the learning curve.
AVAproject may look like Excel, but that’s where the relationship ends. All of AVAware’s products (including AVAproject, AVAcad and AVAproject Fusion) were developed and coded from the ground up by AVAware’s developers. NONE OF AVAWARE’S PRODUCTS ARE BUILT ON OR ARE DEPENDANT UPON ANY OUTSIDE APPLICATIONS. Each product is completely standalone and doesn’t require any other applications in order to run. This is an important consideration, as none of these products is reliant on the support or continuing development of any third party applications. Moreover, AVAware develops all of its own software in-house. As a matter of policy, no outside contractors are ever used in the creation of our products.

|
Is the AVAproject database “relational”?
|
This is one of those “non-questions” that doesn’t have a “yes” or “no” answer. To begin with, one must understand what a “relational”
|
database actually is. This simply means that the data in the database is organized in multiple tables that are “co-related” by one or more common fields. A simple example would be a list of customers and a list of invoices. If both tables contain a “Customer ID” field, or something similar, then the data in the two tables can be matched up by the common “Customer ID”.
This may not seem particularly exciting or innovative, but is definitely was when it was first created – in 1969. This method of organizing data was first proposed by an IBM computer scientist at a time when most databases consisted of little more than single tables. When the first professional database applications became available on PCs in the 1980s, many of them billed themselves as “relational” databases. One of the first (and most popular) was called dBase; it not only brought relational databases to the PC platform, but also offered its own programming language with which simple database applications could be built. This type of product is still being made today and is often used by “developers” with limited time or programming skills to quickly create their own data-centric applications. Developing “applications” inside a database application, made it unnecessary to learn the complexities of programming an actual language such as C, C++ or BASIC.
The greatest downside to this approach, beyond the fact that the scope of the applications was extremely limited, was the dependency on the database product itself. If the database product suffered from “bugs” or became obsolete, so did the applications created with it.
As far as AVAproject is concerned, it uses a variety of different file formats to carry the many types of data that it uses and creates. Project files, Fusion files, hardware catalogs, door & frame catalogs all have different file formats based on their specific needs. AVAproject is not built on top of or constrained by the limits of any one database architecture. File structures and methods of data organization were selected to best suit the given task. Certainly many aspects of these many files contain “relational” components; in addition to hierarchical and indexed as may be the case.
In this day and age, virtually every modern database allows “relational” data organization. Boasting about having a “relational” database today is as ridiculous as bragging about your car having a radio.

|
Does AVAproject run on a network?
|
Of course AVAproject (as well as all of AVAware’s other products) can be used in a network environment. The real question is whether we force you to.
Traditionally, business applications have been designed around a client/server model. This simply means that all the application’s data, and sometimes the application itself, resides on a network fileserver. This approach has its roots
|
back in the earliest days of computer technology with mainframes and mini computers; these systems were built around a central unit that contained all the “intelligence” and functionality. Users interacted with the system by way of “dumb” terminals; in most cases nothing was actually installed on the terminal themselves, they simply provided a conduit to the central machine which did all the work.
For the most part, this model has been abandoned - a long time ago. Not only is it far more efficient to distribute the work load amongst the users PCs, but distributed processing provides an incredible level of “fault tolerance”. When all of a company’s users are tethered to a central server (for processing or just data) they are dependent on it. The moment that server (or the connection to it) goes down, work stops. The users’ PCs are useless without a connection to their “mother ship”. Moreover, if an employee wants to work from home (or any other remote site), they’ll have to maintain a constant VPN (Virtual Private Network) connection back to the server. Aside from the cost, which can be considerable, software performance can suffer if the internet connection becomes slow or unreliable.
That having been said, networks have a number of advantages that will always make them an important part of any enterprise. The ability to collaborate and share data is an essential part of modern business operations. AVAware has taken a contemporary approach to file management on the network. All AVAware products utilize discrete files as a means to hold data. This has a number of huge benefits; files are portable – meaning they can be shared between users as easily as sending an email. Employees wishing to take work home can still use their VPN connections if they wish, but they can also email their project files to themselves or load them on a “thumb” drive. When they are finished their work, they simply upload a copy of the project to the company’s server and make it available to anyone else who needs access to it.
Microsoft has recently been aggressively promoting their SharePoint product. Amongst its many other features, SharePoint allows for the management of discrete files in a network environment. Microsoft has recognized that the traditional server-centric database model is extremely limiting and not ideal for all applications. Several AVAproject users currently utilize SharePoint to manage the flow of project files between users on the corporate network – even in multi-location operations.
The bottom line on networks is this: AVAware offers users the both of both worlds. Users are free to warehouse their data files locally or on the network as desired. Even source data (i.e. product catalogs) can be kept on users’ local machines or in a shared network repository. AVAware does not “pigeon-hole” their users into a single organization model. Obviously, every company is different and has different needs.
|
Ensuring your PC is Running Optimally
|

|
As another year comes to a close, many businesses and individuals alike take advantage of the opportunity to do a bit of housekeeping to get ready for the new year. A tidy desk, clean work space and properly organized paperwork are all wonderful things to come back to after the holiday break to maximize productivity and efficiency. But what about your PC? The following are a few basic PC maintenance tips and tricks to ensure your computer is performing optimally.
|
|
Installed Programs
Throughout the year, many programs may be installed on a computer for a variety of reasons. These programs may include major business applications such as the AVAproject Suite, Microsoft Office, Adobe Acrobat, etc. These are examples of trusted applications that are likely among the most important applications installed. Other programs may be software that was installed for a specific isolated task such as file converters, download managers, registry cleaners, media players, support assistant applications or an endless number of system "utilities". There also may be applications that have been installed unintentionally or even secretly during the install process of other applications or through malicious web sites. These programs
|
may actually be set to run as background processes automatically when the computer is started, consuming system resources right from startup to shut down.
Clearly, it is important to be sure the computer's resources (processor, RAM, hard drive, etc.) are as available as they can be for the most important applications. This maximizes the speed at which these programs can perform and therefore provides the best possible user experience. Additionally, there is no easy way of telling what data malicious programs running in the background are collecting and where or to whom they are sending it.
For the reasons stated above, it is good practice to review the installed programs list once in a while and
|
remove anything that appears suspicious or is not recognized. The installed programs list can be found in the Control Panel under "Programs and Features" in Windows 7 (In earlier versions of Windows such as Windows XP, it is called "Add/Remove Programs"). "Free" Games and Toolbars are major offenders of installing additional software or reporting on usage data, searches, activity, etc. Simply think, if I were a software developer and spent months developing this application, how could I offer it for free?
|
NOTE: If unsure about a specific program, always consult your IT department and/or consultant. Removing important system tools or components may prevent software from running properly.
|
|
|
Startup Programs
The "Programs and Features" tool in the Control Panel lists software that was installed by a Windows Installer (a standard method of installing software). These programs, as mentioned previously, have an Uninstall capability. There are, however, other programs that do not offer an Uninstall process that may be running. To review and/or disable these programs, there is a little inconspicuous tool available called "System Configuration".
|
NOTE: This tool makes changes to the way the computer starts up. Use this tool at your own risk and with extreme caution. If in doubt, speak to your IT department or consultant.
|
|
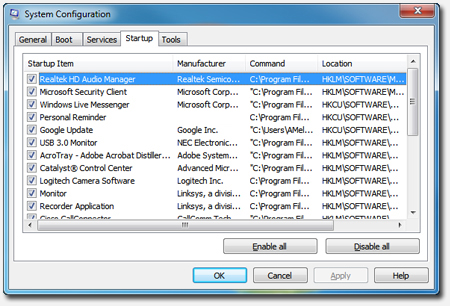
The Windows System Configuration Utility, 'MSConfig'
|
|
To use the tool, use the "Run..." option in the Start Menu. When prompted, type "MSCONFIG" in the dialog and click "OK". Under the "Startup" Tab, software that is set to run when Windows is started is listed. Many of these entries will be legitimate and necessary, but with a discriminating eye one can spot the problem software.
|
Look for items that do not have a manufacturer listed, a bizarre or unreadable name or no name at all. Also examine the "Command" path to be sure the program and its function are recognized and trusted.
To disable an item, uncheck the "Startup Item" and click "Apply". When finished, click "OK". The System
|
Configuration tool will ask to reboot the computer, as the programs that have been set to be disabled are still currently running. Once the system has rebooted, a small dialog will be shown as a notification that the startup configuration has been changed.
|
|
Temporary Files
Temporary files are a major contributor to problems with disk space. On computers that are rarely cleaned up, there are often many gigabytes of disk space being occupied by temporary files such as downloaded application installers and locally cached web sites. These files are not important to the proper function of the system, however there are some cases where it may be desirable to make backups of certain temporary files. AVAproject, for instance, saves copies of project files in temporary directories as backups in case of system failure or file corruption (if the "Auto-Save" feature is enabled).
|
NOTE: If AVAproject's "Auto-Save" feature is enabled, the saved copies of project files can be accessed by opening AVAproject and selecting the "Open from TEMP Directory" option from the "Help" menu.
|
|
To remove temporary files from your system, Windows offers a very simple tool called "Disk Cleanup" and can be found in the Start Menu under "All Programs" / "Accessories" / "System Tools". With this tool, simply select the drive to clean up (typically "C:" - the system drive) and click "OK". The tool will look in all of the various places temporary files are saved and present a list of options and areas to clean. Again, removing any or all of these files should not negatively affect any of your programs, but if in doubt, always talk to your IT department or consultant.
Browser Add-Ons
Browser add-ons are small programs that run inside of web browsers such as Internet Explorer, Firefox, Chrome and many more. Often they cause the browser to run slower than usual, and in some cases also pose a security risk
|
by reporting usage data and tracking activity and search terms back to the developers of the add-on.
As with installed programs, some of these add-ons were likely installed intentionally such as the Adobe Acrobat Reader which allows PDF files from web sites to be displayed in the browser. Other add-ons may have been installed unintentionally or maliciously.
To review and/or disable browser add-ons in Internet Explorer, under the "Tools" icon, click "Manage Add-Ons". There is very little risk of causing any problems to your system by disabling browser add-ons, so if your browser is sluggish, it's quite acceptable to disable all add-ons and selectively re-enable desired items until the major culprit is identified.

|
|

|
Windows Update
|
Virtually every piece of software will inevitably have updates made to it. These “updates” can be for a number of reasons, ranging from new feature to addressing “bug” issues and security threats. Though often overlooked, the same holds true for the operating system itself. Microsoft also releases regular updates to Windows for all the same reasons.
If Windows (and other Microsoft software) is not current with the latest bug fixes and patches, your system is vulnerable to viruses, spyware and other malicious software. Windows
|
Update is a built-in software download and installation system for keeping Windows and other Microsoft products up to date. Windows Update not only ensures the latest operating system and program features are available, but also provides the latest bug fixes and security vulnerability patches that are critical for system safety. The software updates come directly from Microsoft and may be trusted for installation.
In the Windows Update preferences the system administrator can set whether Windows Update should download and install updates automatically, simply download the updates and wait to be instructed to install them, or neither download nor install updates. If the second or third option is selected,
|
respectively, it is extremely important that the user manually install the latest Windows updates on a regular basis.
Many malicious software preys on “un-patched” computers, as the vulnerabilities they exploit are often already patched via Windows Update. We recommend downloading and installing updates automatically if possible, since it keeps the operating system and software up to date constantly and provides the best protection against the latest threats.
To change preferences and/or install updates, simply locate and run “Windows Update” in the “All Programs” section of the Start Menu.
|
|
As a final note, it is always advisable to be using anti-virus / anti-malware software to protect your computer from malicious programs. Some of the traditional anti-virus suites actually consume a lot of system resources in their own right, which may be bogging your computer down. Microsoft offers their own (free) program to combat malicious software called Microsoft Security Essentials. We have found it to be very light-weight in terms of the required system resources and just as effective as other commercial solutions.
|
|
AVAproject and AVAcad have always been known for their powerful CAD and graphics capabilities. From the beginning, however, AVAproject has innovated the process of creating architectural hardware specifications by offering tools and methodologies never before seen in the industry.
In last month’s edition of AVAwire, the AVAproject tip focused on creating the “skeletal” structure of a hardware schedule from the architect-provided plans or openings list. Unlike traditional headings-based take-offs, AVAproject and its openings-based approach allows estimators to enter and manage project data with unmatched flexibility.
In addition to being able to enter information in virtually any sequence, data entered for one aspect of a project can be easily reused for others. A clear example of this is the way that information entered into the Openings Schedule can be used to create the foundation for a Hardware Schedule. In the past, hardware estimators would have to enter openings-related information in headings that would also be entered by door and frame estimators in the Openings Schedule. Along with the cumbersome repetition of labor, came the inevitable errors and omissions that always occur despite everyone's best efforts. AVAproject puts an end to this by allowing people to “recycle” the work of their counterparts. In addition to eliminating countless hours on the keyboard and all those costly errors, another traditional source of problems is gone forever; Never again will hardware and openings estimators fall “out of sync” with each other when one fails to inform the other of changes to the project
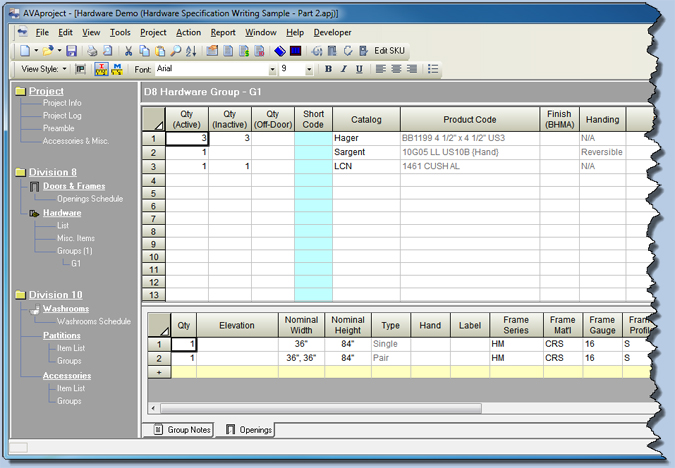
AVAproject's Hardware Group Editor with Openings Schedule visible below
Once the openings list has been entered, the specification writer can begin the task of assigning hardware products to them. Amongst the many innovative tools offered by AVAproject, there is one in particular that can shave hours off the time required to build a hardware specification.
Create Multi-Purpose Hardware Groups
Hardware Groups are a unique and powerful shortcut for creating hardware specifications for projects that contain a number of similar openings. As their name implies, these are groups of hardware products that are used on one or more given openings. Although they certainly can, hardware groups do not necessarily have to correspond to headings. This is an important distinction between the two. It is possible to assign the same hardware group to different openings that will eventually appear on different headings in the hardware schedule.
The obvious question is: Why would anyone want to do this? The answer is simple: To save a lot of time.
There are several simple examples: Openings with different sizes, material and label requirements are often separated into different headings. Standards vary between spec. writers and architects, which is why AVAproject has so many granular grouping options. The fact remains however, that no matter how openings are separated there will be instances when the same hardware mix will appear on different headings. It’s in cases such as this that AVAproject can save a tremendous amount of time.
In addition, AVAproject allows the same hardware groups to be used for single and paired openings. By splitting quantities between active and inactive leafs, the system can adjust the product mix to accommodate the openings it is assigned to. Once again, this can save a tremendous amount of time by reducing the number of groups that need to be entered and maintained.
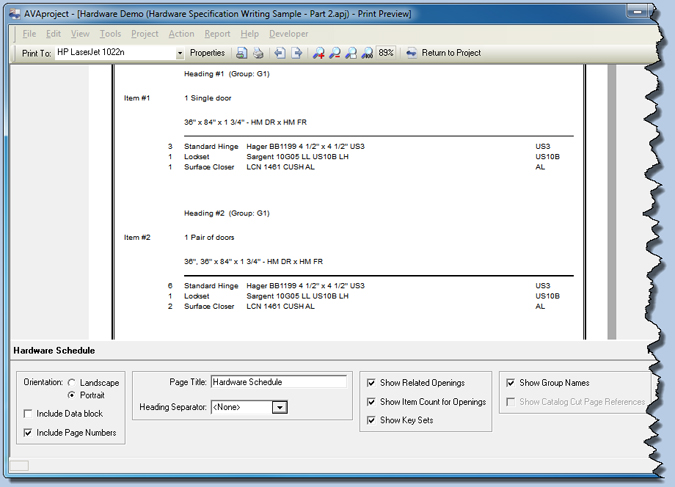
An AVAproject Hardware Schedule Report generated from the Hardware Group pictured above. Notice that two headings were created
automatically (with appropriate quantities) using the same Hardware Group on different openings - one single and one pair.
|
|
|
We welcome any questions, comments or suggestions about any topic mentioned in this edition of AVAwire. Please visit our website for more information, or contact us directly at (416) 239-9099.
|
|