
Cloud Services Hacked & Social Engineering Reveals Massive Security Failures
Powerful Export Tools Allow Nearly Limitless Software Integration
DHI 2012: It's That Time of Year Again
Stanley Canada Rolls Back 2012 Printed Catalog Due to Errors
AVAware Tip: Securing Your Data in the Clouds
|

|

|
Cloud Services Hacked & Social Engineering Reveals Massive Security Failures
|

|
In a recent issue of AVAwire, we discussed several causes for concern and areas or potential risk for those who relied on cloud-based services to store their vital data. Not to say “we told you so”, but several service providers have recently experienced instances of “hacks”’ and other of “security failures”!
|
|
The past month has not been kind to the cloud. Several popular online services have reported incidents of “hacking”, some resulting in substantial data loss for unfortunate users.
|
|

| 200,000 LinkedIn Passwords Reported Cracked 1 |
In early June, Vicente Silveira, Director at LinkedIn confirmed that 200,000 passwords had been hacked and reportedly sent emails to the owners of all the compromised accounts giving details and instructions on how to reset their passwords. Users were advised to not only change their passwords on LinkedIn, but on any other service where they used the same ones.

| Reuters’ Twitter account hacked 2 |
The Reuters news organization reported that their Twitter account (@reuterstech) was commandeered by hackers and used to disseminate pro-Syrian government tweets. No details were offered as to how this was done, but the account has been suspended pending a complete investigation.

| Several Hundred Dropbox Accounts Hacked 3 |
On July 31st, the popular cloud-based storage service Dropbox reported that
|
hackers had accessed data in several hundred unsuspecting Dropbox users’ accounts. It was suggested that third party sites were responsible for allowing malicious individuals to gain access to usernames and passwords that allowed them to sign in to the various DropBox accounts.

| A Call to Apple Support Results in a New Father Losing Photos of His 18-Month Old Daughter! 4 |
Although only one person was affected, perhaps the most devastating hack in recent times was a lesson in dangers of “Social Engineering”. Gozmodo techology journalist, Mat Honan was playing with his baby daughter when suddenly his iPhone, iPad and Macbook computer all suddenly went dark! It seems a hacker obtained information through phone calls to Amazon and Apple technical support that allowed them to gain access to several of Honan’s online accounts – including his Apple ID. All this was done in an effort to hijack Honan’s enviable 3-character Twitter handle (@mat).
In order to prevent him from resetting his own password and ensure that there was sufficient time for the hacker to complete the task, the hacker used Apple’s ‘remote wipe’ feature to
|
completely empty the contents of all his connected devices and his iCloud backups.
The really unfortunate result of all this was the loss of all the pictures that the new father had taken of his 18-month old daughter thus far. Reportedly, all his accounts have been restored but the pictures have not.
The reason we’re bringing these incidents to the attention of our clients is simply this – to demonstrate that IT DOES HAPPEN! All of these hacks occurred in just one month and there’s no telling how many other incidents may have occurred in the same time period. It’s only because of the rising trend in online computing that stories like these are getting reported at all.
We realize that articles (such as the one we published recently outlining the potential pitfalls associated with cloud computing) can appear somewhat pessimistic, but the reality is: These things do happen. Not only do they happen, but they are doing so at an increasing rate.
Users must recognize that cloud-based computing is a brand new technology and should consider the possible ramifications carefully and take the proper precautions before entrusting sensitive or confidential data to such a service.
|
|
1 Source: “LinkedIn Confirms Account Passwords Hacked”, Ian Paul, PC World, Jun 6, 2012
2 Source: “Reuters Twitter account hijacked, fake tweets sent”, Steven Musil, cnet.com, Aug 5, 2012
3 Source: “Dropbox confirms it was hacked, offers users help”, Dana Kerr, cnet.com, Jul 31, 2012
4 Source: “Allowed Hackers Access To User's iCloud Account”, forbes.com, Aug 5, 2012
|
|
In virtually all modern enterprises, software integration, or the ability to move data between systems and applications is absolutely essential. For most businesses, data is only as useful as their ability to make it available wherever it’s needed. Although there may have been a time where an entire operation would rely on a single application for everything they do, like DOS - those times are behind us!
The fact is there are countless powerful and robust enterprise applications ranging from simple
|
accounting to data mining and complex reporting. These last two items fall into the newest category of enterprise tool – “business intelligence”. Simply put, this involves analyzing existing and supplementary data to form the basis of better business decisions. This is where AVAproject Fusion truly excels.
Data Harvesting
Whether one intends to create a custom report, a pivot table or a data export, the process begins with
|
selecting the relevant data from the entire project (or group of projects). Fusion facilitates this by way a revolutionary “filter builder” that allows any user to build data queries using a simple linguistic interface. Normally this task would be left to programmers or other I.T. (information technology) personnel, but Fusion makes it possible for users to do it for themselves – often in seconds.
|
|
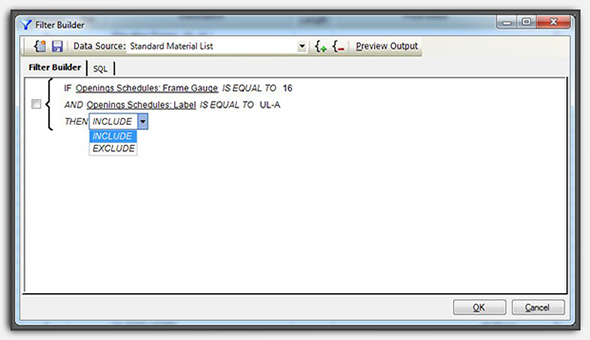
The AVAproject Fusion Filter Builder
|
|
Use the Data In Many Ways
Once a filter has been created in Fusion, the resulting data can be used for a variety of tasks. The same data can instantly be used for:
- Reviewing on-screen with user-definable grouping, sorting and column layouts (grid view)
- User-designed reports, also with user-definable grouping, sorting and column layouts
- Complex ‘pivot tables’ that place user-specified data on an X-Y table of values
- Exporting data into a variety of supported file formats
|
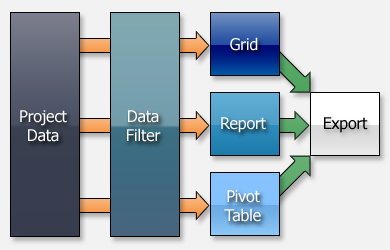
An Illustration of Data Flow in AVAproject Fusion
|
|
All of these tasks would have necessitated a call to an I.T. professional with all its associated costs and development time. AVAproject Fusion has placed this power into the hands of the users; tasks can now be accomplished in less time than it would normally take to explain to a programmer to get it done. Moreover, the entire cost of the Fusion product can be recovered in the cost of the first custom report that is created.
According to Chris McNeilly of Upper Canada Specialty Hardware in Toronto, Ontario: “AVAproject Fusion has allowed us to create custom queries and reports that meet
|
our specific business needs. The templates created for the reports and data filters help us reproduce the same results from project to project. Multi project analysis is a snap and allows us to quickly view and sort through data across a practically unlimited number of projects.”
Other users have successfully used AVAproject Fusion (without any additional custom modules) to move data from AVAproject directly into their accounting system. Recently, Jeff LeBrun of Construction Technologies Inc. in Dartmouth, Nova Scotia has utilized the advanced CSV file creation tool built into Fusion to export data into their cloud-based Netsuite accounting
|
platform. Once again, this effort required no outside programming or additional software.
AVAware’s team of experts are always available to discuss how AVAproject Fusion can be used to effectively integrate your company’s project detailing, estimating and management processes into your accounting/ERP system of choice.
Absolutely no other industry software package offers anything close to this level of power and flexibility!
|
|
If anyone ever needed a good reason to take a few days off from their daily office grind, what could be better than a few days in fabulous Las Vegas?
The Door and Hardware Institute (DHI) has rebranded their long established annual convention event this year. No longer shall it be referred to as simply the “DHI Convention”, it shall be hereinafter referred to as “CoNEXTions” or “DHIndustry Convention”. (At least it will be by anyone clever enough to figure out how to pronounce these new linguistic constructs.) Unpronounceable naming aside, the DHI is signaling changes ahead for the annual gathering, and changes are exactly what are needed.
This well-established event has been devastated by a series of mergers and acquisitions that have occurred throughout the architectural openings
|
industry over the past decade. Companies such as Assa Abloy and Ingersoll-Rand have consolidated groups of manufacturers that used to represent well over a dozen separate booths into only one each. This, in addition to the recession of recent years, has left the DHI Convention a mere shadow of its former self.
Long-time attendees will remember much-anticipated social events such as Hager’s Saturday night extravaganzas and the late Friday night hospitality suite circuit. These traditions may have been lost to the convention’s abbreviated schedule of recent years, but a leaner and meaner may be exactly what the current business environment requires. The new DHI convention format is all business and that’s precisely what attendees are looking for. It’s during times of economic uncertainty that successful
|
businesses rely on the relationships they have cultivated and those yet to be built.
For those who haven’t yet made the decision to attend, there is yet another important consideration; due to scheduling issues, the DHI has no convention planned for 2013. It’s even more important than usual to make an effort to attend, as this may be that last opportunity many people will have to meet their peers in person until 2014.
AVAware will be present on the show floor in booth number 1135. As always, we are looking forward to visits from our valued existing clients as well as those we haven’t yet had the pleasure to meet.
We look forward to seeing you all in Vegas!
|
|
Shortly after the release of Stanley Security Solutions printed 2012 Commercial Hardware price list and the subsequent release of the corresponding AVAware electronic version, we received an email from Stanley indicating that they had found a number of errors in the printed document. According to William Munkres (Stanley’s Channel Manager for Commercial Mechanical Access Solutions) Stanley intends to completely redo the book in order to eliminate any confusion amongst their customers.
|
Upon receiving this notification from Stanley, AVAware removed the electronic version of this price list from our website and replaced it with the prior year’s edition. Users of the Canadian Stanley catalog should ensure that they are not using the June 25, 2012 release (rev. 61CH). Please verify that you have removed that catalog from your Repository and reinstalled the previous release (rev. 58CH, dated April 6, 2009). If you require any assistance with re-installing the previous release, please contact our support department.
|
Stanley has advised us that the updated version code for the corrected 2012 price list will likely be 61CH_A. AVAware will update the electronic catalog as soon as we receive the updated document from Stanley. As always, AVAproject will automatically notify catalog users when an updated version is available.
|
|
Normally this section of AVAwire is dedicated to showcasing tips and techniques aimed at assisting users of AVAware software work even more efficiently. Given the recent security issues experienced by various online and cloud-based services, we thought it appropriate to offer a bit of a departure from our usual fare.
|
A Brief History of Hacking...
We’ve all seen that character in every crime drama – the one that can “hack” into anything from police computers to elevation control systems in a matter of seconds. Good news: such a person does not actually exist. Hacking is more about systematic attacks and “social engineering” than about knowing some super secret sequence of keystrokes that will make a user account pop open faster than you can say “Open Sesame!”
Systematic Attacks (a.k.a. The “Brute Force” Method)
|
The classic brute force approach to discovering a password involves nothing more sophisticated than a library of common words,
names and phrases that hackers will attempt against a given user name in every possible combination. Resourceful hackers will even “customize” attacks on individuals by adding words, names and dates that they know relate specifically to the person they are targeting.
Social Engineering
|
The most common (and completely non-technical) approach to discovering user names and passwords is referred to “Social Engineering”. This is simply a fancy way of saying “tricking someone into letting you in”. Classic forms of this “hack” involve people calling unsuspecting users and claiming to be a support person, a co-worker from another location, a bank employee, etc. It is surprising to find out how many people are willing to provide confidential information if just asked the right way.
A type of “game” is played every year at the annual DefCon hackers’ convention in Las Vegas. A “hacker” is
|

|
placed in a sound proof booth and given a specific amount of time to call various business and attempt to trick the people at the other end of the phone into providing access to user accounts. They are always successful, and always in a matter of minutes!
Given this information, the real question is “What can a person do to protect themselves?” The following is a short list of simple ideas that can help protect your online presence from becoming the victim of a hacker. Please bear in mind, although some of these ideas may seem obvious – if more people actually took these precautions there would be fewer security breaches.

| Use Secure Passwords |
Your password is your first line of defence against the simplest form of hacking. Experts suggest using passwords with at least 10-12 characters, being sure to combine numeric as well as alphabetic characters. Also, don’t be afraid to incorporate symbols (+-/#$%&) into your password whenever they’re allowed by the system you’re securing.
Be certain to avoid names and dates that are specific and personal to you. If you know them, then it’s likely that other people will as well. Celebrities have had their accounts hacked because they’ve used names for passwords that could be found on fan sites and Wikipedia!
Also, remember those resourceful hackers that will add your personal information to their systematic attack libraries. If you think that simply combining your spouse’s name and your mother’s birthday results in an unbreakable password – think again!

| Lie on the "Security" Questions |
Many systems (i.e. banks) use secret security questions to verify your identity. Most will let you select the question, though most offer a list of acceptable choices. The problem is that the questions usually have answers that anybody who knows you will also know the answers to. Questions like “Where did you go to school?” and “What is your mother’s maiden name?” are NOT secure. You are far better off deciding on a fictitious answer that no one else would ever guess and use that. Remember, no one insists on the answer to these questions being true – they only have to match the answers you gave when you set up your account.

| Use Multiple Passwords and Email Accounts |
The biggest mistake most people make is to use the same password on multiple sites and accounts. This is never a good idea. Obviously, should a hacker get lucky and gain access to one of your accounts, they suddenly have access to all of them.
Most systems require you to provide an email address that they can use to send password reset links when necessary. Do not use the same email address for all your accounts for the same reason you wouldn’t use the same password. If a hacker gets hold of your email account, they can request password resets for every system for which you’ve used that email address to setup an account.

| Use "Two-Factor" Identification Where Available |
Simply put, “two factor” identification requires two pieces of information to log into a given account. Usually this is a password and a numeric code that is either sent to your phone via SMS or a rotating number that you are given ahead of time.
This type of login is certainly more inconvenient, but infinitely more secure and virtually unbreakable!

| Educate Your Friends and Employees |
The only line of defence against social engineering is education. Meet with your staff and discuss this growing trend; make sure they know not give out confidential passwords to ANYONE they don’t know, no matter how good the story sounds. Remember, these types of hackers are experts and have surprisingly good results even when dealing with intelligent people!
Beyond that, make sure everyone you know knows that companies like Microsoft and especially your bank will NEVER phone up and ask for a password... EVER!

| When All Else Fails... BACKUP, BACKUP, BACKUP! |
Despite everyone best efforts, sometimes the unfortunate happens. When it does, the only thing you have to fall back on is often secure backup copies of your data.
Effective backup practises is a topic for its own article, but briefly there are a few things to keep in mind. The ONLY form of backup that can never be hacked is one that NOT connected to anything. For that reason, never rely on any cloud-based storage solution as your only backup. Removable hard drives cost less than a hundred dollars and will instantly become priceless should you ever find yourself staring at an empty hard drive or cloud account.
With all that said, always bear in mind a little paranoia can be a good thing. Although security often comes at the cost of convenience, please consider the implications to your business and your life in general should you become the victim of a hack.
|
|
|
We welcome any questions, comments or suggestions about any topic mentioned in this edition of AVAwire. Please visit our website for more information, or contact us directly at (416) 239-9099.
|
|